ROSS ULBRICHT DESERVES A SECOND CHANCE
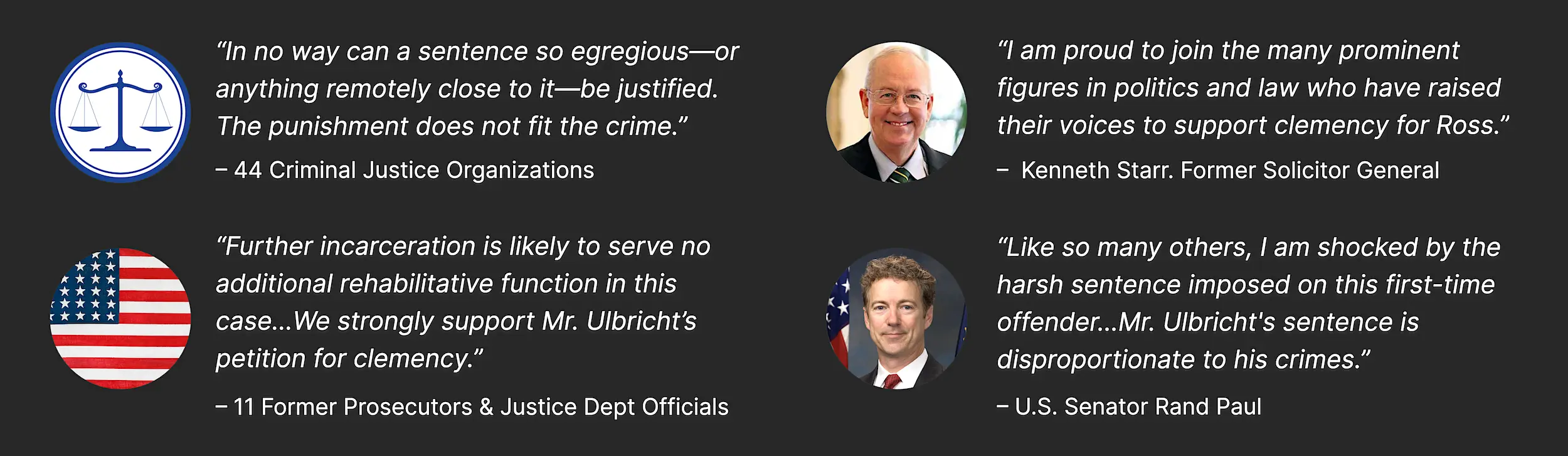
WIDESPREAD SUPPORT FOR CLEMENCY
There is a strong, bipartisan consensus that Ross’s sentence is unjust and that he deserves a second chance.
Over 250 organizations, eminent individuals & leaders have voiced support.
- In prison since 2013
- First-time offender
- All non-violent convictions
- Two life sentences + 40 years without parole
Ross Ulbricht is condemned to die in prison for creating an anonymous e-commerce website called Silk Road. An entrepreneur passionate about free markets and privacy, he was 26 when he made the site. He was never prosecuted for causing harm or bodily injury and no victim was named at trial.
Users of Silk Road chose to exchange a variety of goods, both legal and illegal, including drugs (most commonly small amounts of cannabis1). Prohibited was anything involuntary that could harm a third party.
Ross was not convicted of selling drugs or illegal items himself, but was held responsible for what others sold on the site.

“Over countless hours, I have searched my soul and examined the misguided decisions I made when I was younger. I have dug deep and made a sincere effort to not just change what I do, but who I am. I am no longer the type of man who could break the law and let down so many.”
– Ross Ulbricht in letter to the President [PDF]
SMEARED WITH FALSE ALLEGATIONS
Ross consistently denied the allegations (which relied on anonymous online chats never proven to have been authored by him) and those who know him never believed them. The only alleged victim ever identified, Curtis Green, is a fervent supporter of Ross’s clemency.
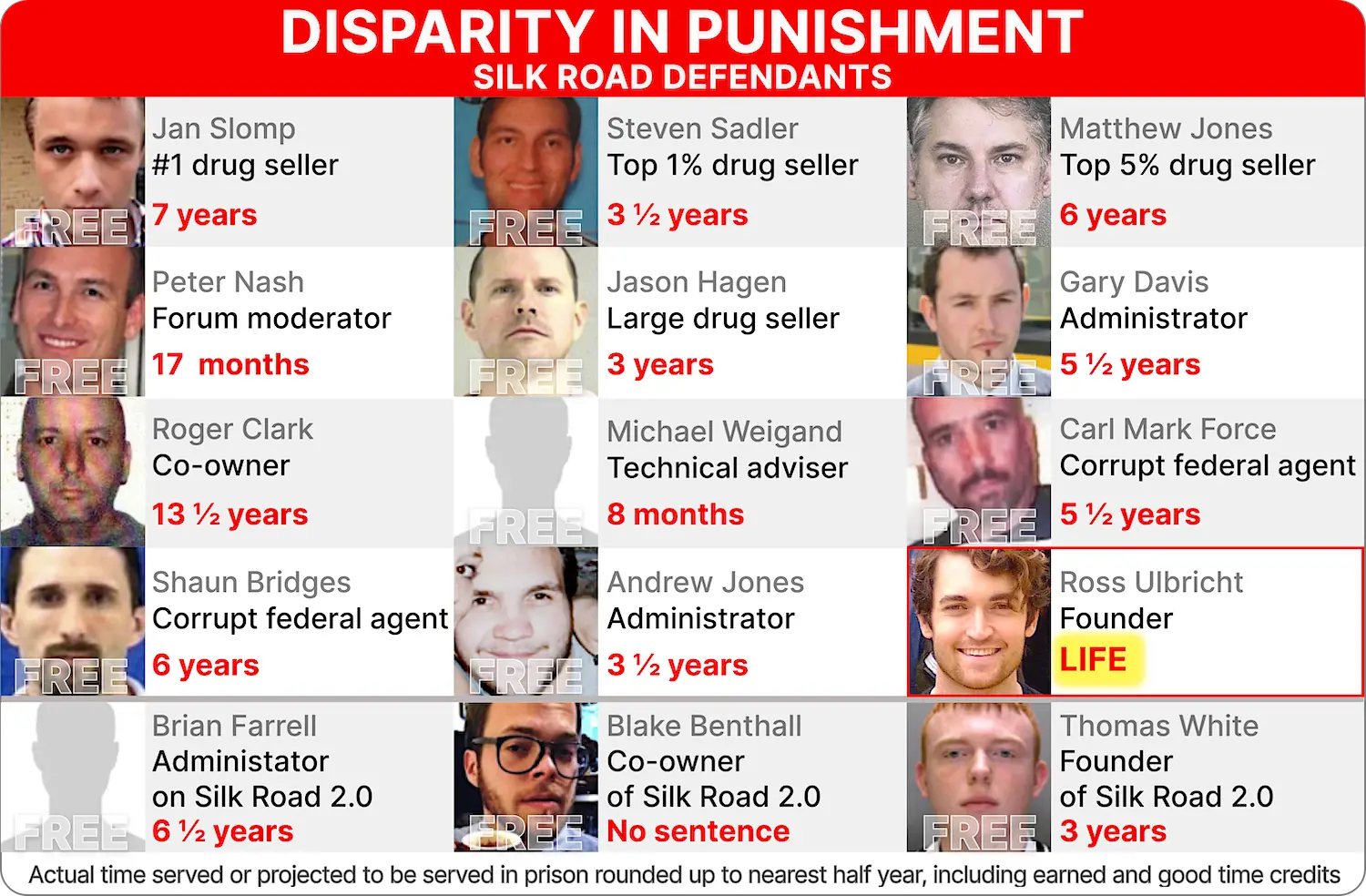
EXTREME SENTENCING DISPARITY
Ross Ulbricht’s sentence implies that he can never be given a second chance for as long as he lives, regardless of his rehabilitation and attempts to make amends.
The average prison sentence all the other defendants related to the case received is six years, including the actual drug sellers, the men who helped run Silk Road, and the men behind Silk Road 2.0, a larger replica. All but one are free today.
“Such a sentence should, at the very least, be reserved for the worst crimes committed by repeat offenders…Ross’s crime is nowhere near that category and his sentence is grossly excessive.”
– Shon Hopwood. Law Professor, Georgetown University
EXEMPLARY CONDUCT

Ross has taught science and math classes, and tutored fellow prisoners. He has led yoga and meditation classes to help prisoners better cope with anxiety. He currently leads support groups and serves as a mediator within his unit.
Over 150 former and current fellow prisoners have signed letters and written testimonials attesting to Ross’s good influence and supporting his clemency.
MAKING AMENDS
With a focus on lowering recidivism and harm reduction, Art4Giving has donated, in large part, to charities that support prisoners through prison visits, education, and successful re-entry and to charities that provide drug addiction prevention and treatment.
So far, over $750,000 has been donated to charity, thanks to Ross’s art.

WE NEED YOUR HELP TO FREE ROSS ULBRICHT
Ross Ulbricht was an idealistic entrepreneur who never intended harm. He deeply regrets and has taken responsibility for his actions. He has learned his lesson the hard way. If released tomorrow, he would never break the law again.
Ross clings to the hope of a second chance and dreams of a future where he can start a family with his fiancée and make positive contributions to society.
We are just regular people working every day to get Ross some relief.
Please join us in freeing Ross!
▲ 1 – Researchers at Carnegie Mellon University conducted a comprehensive analysis of Silk Road, gathering and analyzing data on a daily basis for eight months before the site was shut down. Some of their findings include:
“‘Weed’ (i.e., marijuana) is the most popular item on Silk Road” (p.8)
“The quantities being sold are generally rather small (e.g., a few grams of marijuana)” (p.12)